
How to Set Up DMARC for Your Domain: The Ultimate Guide
If you own a domain and send emails, you are a potential target for cybercriminals. Without DMARC, anyone on the internet can send an email pretending to be you. With Google and Yahoo now mandating authentication for bulk senders, DMARC is no longer optional.
What you will learn: SPF & DKIM prerequisites, step-by-step DNS setup, policy options (none/quarantine/reject), reading reports, common mistakes, and the enforcement journey.
1 What is DMARC and Why Does It Matter?
DMARC stands for Domain-based Message Authentication, Reporting, and Conformance. It protects your domain from being used for email spoofing, phishing, and other cybercrimes.

The Scale of Email Spoofing
- 3.8 billion phishing emails sent globally every single day
- 90% of cyberattacks start with a deceptive email
- 72% involve brand spoofing - impersonating a legitimate domain
- $4.8 million average cost of a phishing-initiated data breach
Google & Yahoo mandate: Since 2024, bulk senders (5,000+ emails/day) must have DMARC in place or risk being blocked entirely.
2 Prerequisites: SPF and DKIM
SPF (Sender Policy Framework) - The Guest List
A DNS record listing all IP addresses and services authorized to send email on behalf of your domain. If the sender isn't on the list, SPF fails.
v=spf1 include:_spf.google.com include:spf.min8t.com ~allDKIM (DomainKeys Identified Mail) - The Wax Seal
A cryptographic signature attached to every email. The receiving server verifies it using your public key in DNS. DKIM ensures the email wasn't tampered with in transit.
Why DMARC is Still Needed
SPF and DKIM check technical headers, but not the visible "From" address. A scammer can pass SPF/DKIM with their own domain while displaying YOUR address. DMARC adds "alignment" - requiring that the authenticated domain matches the visible "From" domain.
3 Step-by-Step DMARC Setup

Step 1: Audit Your Sending Sources
List every tool that sends email from your domain: email suite, marketing platform, CRM, support tools, transactional services, website forms.
Step 2: Verify SPF and DKIM
Ensure both are configured for every service. DMARC passes if either SPF or DKIM aligns (having both is ideal).
Step 3: Create Your DMARC Record
v=DMARC1; p=none; rua=mailto:reports@yourdomain.com;v=DMARC1- Version identifier (always first)p=none- Policy: monitor only, don't block anythingrua=mailto:...- Where to send daily aggregate reports
Step 4: Publish in DNS
DNS settings: Type: TXT | Name: _dmarc | Value: your DMARC record | TTL: 3600
4 Policy Options: none, quarantine, reject

p=none (Monitoring)
"Check my emails, but deliver them normally even if they fail. Just send me reports." Always start here.
p=quarantine (Warning)
"If an email fails DMARC, send it to Spam/Junk." Use after fixing all alignment issues found during monitoring.
p=reject (Maximum Security)
"If an email fails DMARC, drop it completely." Only use when 100% confident all legitimate sources are authenticated.
5 Reading DMARC Reports
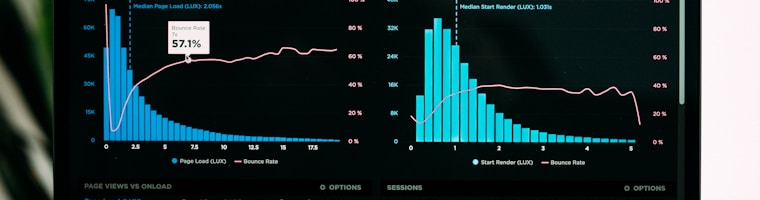
Aggregate Reports (RUA)
Daily XML files from inbox providers showing IP addresses, message counts, and pass/fail results. The problem: raw XML is unreadable.
Forensic Reports (RUF)
Real-time reports for individual failures. Note: Google and Microsoft no longer send these due to privacy concerns.
MiN8T tip: Point your rua to MiN8T's DMARC monitoring. It automatically parses XML into visual dashboards showing compliance rates, sending sources, and alignment issues.
6 Common Mistakes
- Set and Forget: Staying at
p=noneforever provides zero protection against spoofing - SPF 10-Lookup Limit: Too many
include:statements breaks SPF entirely - Forgetting Subdomains: Attackers will spoof
billing.yourdomain.comif you only protect the root - Auto-Forwarding: Forwarding breaks SPF. Rely on DKIM which survives forwarding
7 The Enforcement Journey

- Weeks 1-4 (Assess): Publish
p=none, collect reports in MiN8T, identify all sending sources - Weeks 5-8 (Remediate): Fix SPF/DKIM for every service showing failures in the dashboard
- Weeks 9-12 (Quarantine): Move to
p=quarantine, start withpct=10and increase gradually - Week 13+ (Reject): Full
p=reject- your domain is now immune to exact-domain spoofing
v=DMARC1; p=quarantine; pct=10; rua=mailto:reports@min8t.com;Monitor DMARC Without the Headache
MiN8T's built-in DMARC monitoring parses XML reports into visual dashboards. See compliance rates, sending sources, and alignment issues at a glance.
Start Monitoring Free

